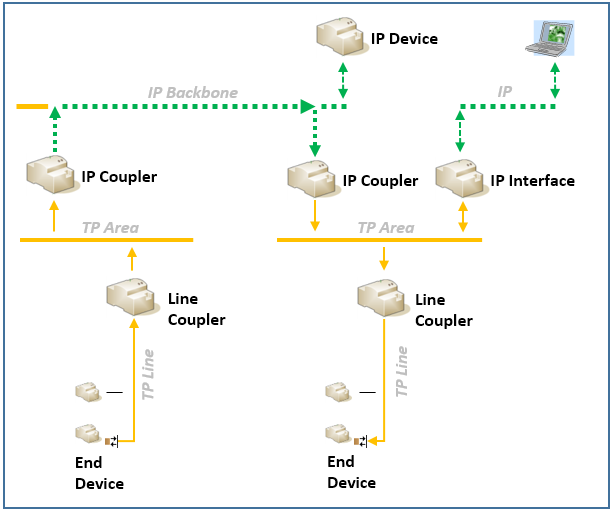
With KNX IP secure only the KNX communication on the IP medium is secure; telegrams on a main line or (sub) line (shown in the image here as a TP line) continue to be plain.
The following KNX Secure devices are indicated as following for differentiation purposes in individual cases.
| Device name | Actions |
|---|---|
| KNX IP Secure coupler | Pass secure telegrams between KNX IP Secure couplers |
| KNX IP Secure interface |
|
| KNX IP Secure device (native IP device with KNX IP Secure) | Send secure telegrams on the IP medium to KNX IP Secure couplers or other KNX IP Secure devices |
The security is defined globally on the topology level. For more information see here. From the device perspective, communication can then be either plain or secured (device:topology = 1:1 relationship).
There are two significant settings:
1. Security activated for commissioning
Commissioning - Device Security
Decision – according to the status of the device security – whether during commissioning (initial commissioning or after a change), ETS should communicate with the device in secured or plain mode.
- If the communication at runtime is secured, then at device commissioning the communication must be secured mandatorily.
- If the communication at runtime is plain, then at device commissioning the communication does not necessarily have to be secured.
2. Security activated for runtime
Runtime - Medium Security
Decision whether communication during runtime should be secured or plain. The topology inherits - in total - the security properties of the KNX Secure devices contained there.
- Automatically (optimally)
- Manually (according to the explicit manual selection of the user)
Both options have impact on the security when inserting devices.
Necessary Keys
All KNX IP Secure couplers (and, as the case may be, KNX IP Secure devices, KNX IP interfaces) operating with secured communication use a shared security key.
- It is created by ETS and is loaded to the KNX IP Secure devices during the commissioning.
- The security key is in general called 'Backbone Key' (also known as 'Multicast Group Key').
- The security key can only be seen in the 'Security' report of a project.
Security properties
The security properties of a device are predefined by the device manufacturer. KNX Secure can be activated/deactivated (at application level).
When KNX IP Secure is activated, then Freshness, Data integrity, Authentication and Encryption are active, which means that the KNX telegram encapsulated in IP is secured in the most important KNX data part (APDU). In this case, the content of the telegram is no longer “readable” by anyone not having the necessary keys.
Telegrams are given a timestamp (runtime) (aka 'consecutive sequential number') and an authentication code (HMAC) and are then encrypted using the following methods:
CCM
- AES 128 CTR for the Encryption
- AES 128 CBC MAC for the Data integrity/Authentication (generation of the HMAC)
Elliptic curve Diffie-Hellman (ECDH, curve 25519)
- Creation of the temporary 'session key' between KNX IP Secure devices and ETS; only used during the commissioning of KNX IP Secure devices by ETS.
Device properties
Depending on the status (enabled/disabled) of the respective device security, a decision is made whether the communication between ETS and the device during commissioning should be secured or plain. Enabling/Disabling the device security is performed on the device in ETS.
Commissioning
KNX IP Secure devices are secured while being put into operation. This comprises the following levels.
- Encryption and Data Integrity (session key)
- Freshness (sequential number)
- Authentication (factory key or authentication code)
- Activation of the necessary device-access level (Management Password)
Necessary Keys
- Are imported via ETS either in advance or on demand (see Adding device certificates)
- Are created individually by ETS for each KNX IP Secure device and loaded to the devices during the commissioning (Authentication Code and Commissioning Password)
- Are saved in the ETS project (contained in the ETS project export)
Factory Default Setup Key (FDSK)
The FDSK is required for the (initial) authentication of KNX IP Secure devices in ETS (device vis-à-vis ETS).
- Every KNX Secure device has an individual FDSK when delivered. This, in combination with the device’s serial number, provides a unique 'physical link' (device certificate) to a device upon delivery.
- The FDSK cannot be modified by the ETS user.
- The FDSK can be seen here in the ETS interface.
Authentication Code
The authentication code is required for the (further) authentication of KNX IP Secure devices (device vis-à-vis ETS).
- Because the FDSK is known outside of ETS, e.g. as a QR code or device label, this key shall be changed in the ETS project
If the FDSK remains known, an authorized device could be simulated using Man in the Middle).
- The FDSK is replaced by a separate (for this ETS and this KNX IP Secure device) authentication code. The subsequent communication of the device vis-à-vis ETS is then performed with this (new) authentication code (instead of the initial FDSK). Consequently, every KNX IP Secure device has a separate authentication code which is different from the initial FDSK after commissioning.
If it has not been overwritten by the ETS user - for several devices - by an identical authentication code.
- The authentication code can be modified by the ETS user.
- The authentication code can be seen here in the ETS interface.
Commissioning Password
The commissioning password is required in ETS for the entire commissioning process for a KNX IP Secure device. It serves also here for the authentication of the ETS vis-à-vis the device.
It shall be different from passwords of possible secured additional interfaces and represents the so-called management level for device configuration by ETS.
The commissioning password is only known to ETS and therefore can make changes on the device (passwords from secured additional interfaces can be distributed, e.g. to an external visualization).
- The commissioning password is assigned during the initial commissioning (for this ETS project and for every KNX IP Secure device). It does not have necessarily have to be different for every device in the project (editable in ETS). Separate commissioning password for each device offers better protection – in the event that an individual key is compromised, or becomes known, this only concerns this one particular device.
- The commissioning password can be seen here in the ETS interface.
KNX Serial Number
- The KNX Serial Number is required in combination with the Factory Default Setup Key during the (initial) commissioning.
- The KNX Serial Number can be seen here in the ETS interface.
Project properties
For project properties and KNX Secure, see here.
